If your sector is being targeted, you’ll know about it before it reaches you.
Who We Are
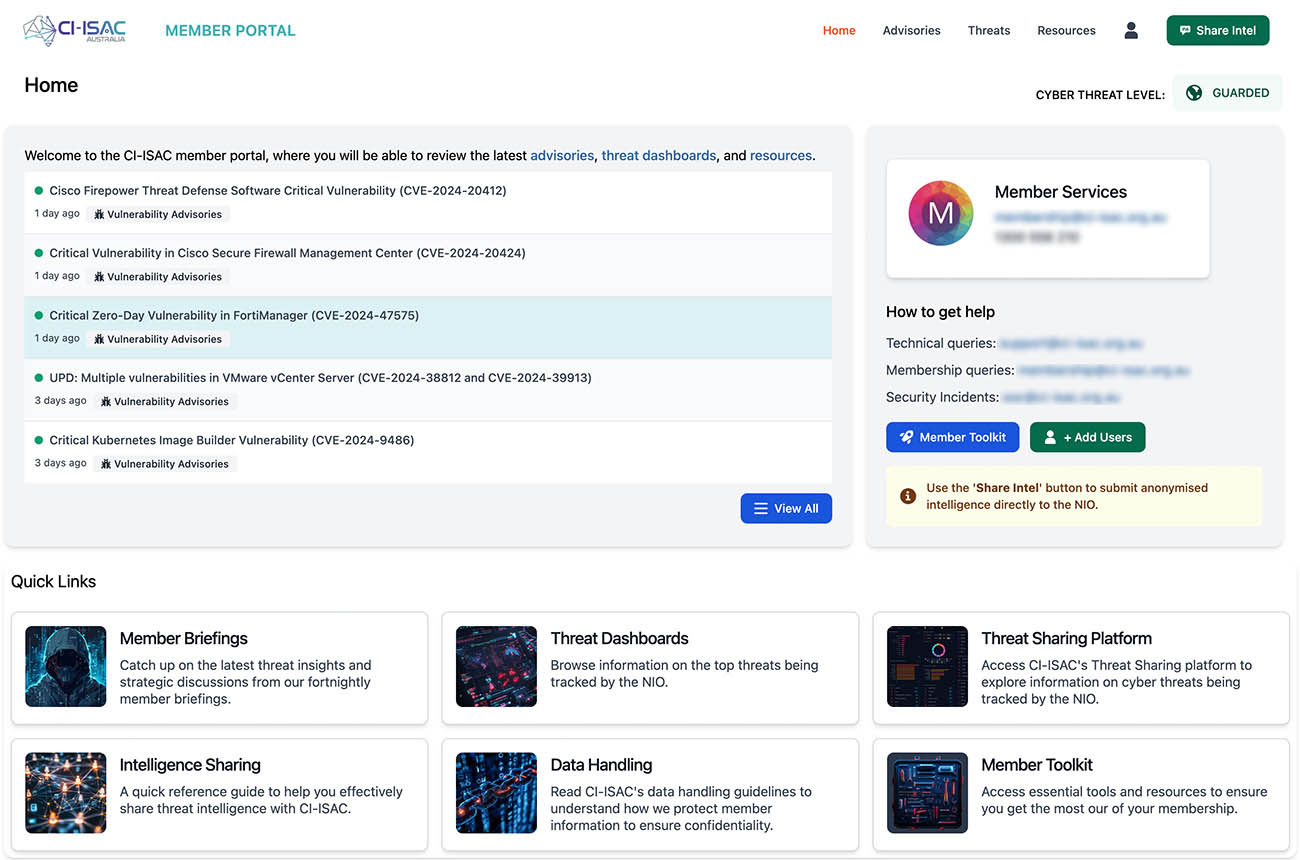
CI-ISAC is Australia’s only sovereign, not-for-profit cyber threat intelligence network built exclusively for critical infrastructure.
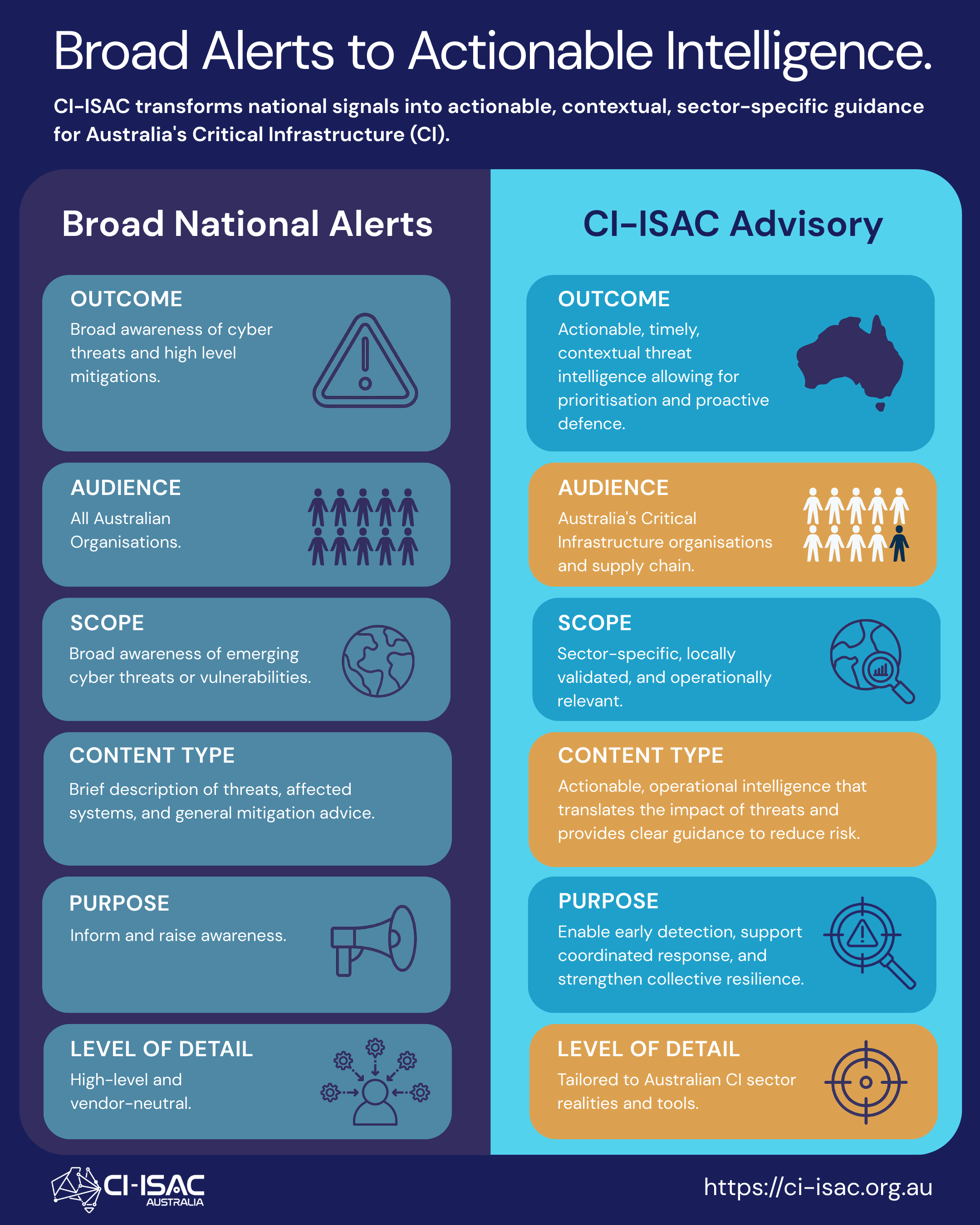
Our analysts monitor threats across all 11 critical infrastructure sectors simultaneously — energy, health, finance, government, telecommunications and more — and turn that raw data into clear, actionable advisories your team can act on immediately.
What We Do
Members contribute what they’re seeing.
We analyse it and enrich it with intelligence from our own Australian honeypots and global sources.
We share it back across the entire network — anonymously where needed.
The result is collective visibility that no single organisation, however well-resourced, can replicate alone.
Membership Benefits
CI-ISAC delivers three key benefits to help members improve their collective defences.
#1
Reduce Risk

Prioritise your security resources by focusing on mitigating the risks that matter most to your organisation
#2
Save Money

Leverage threat intelligence to address the threats relevant to your organisation, freeing up internal resources
#3
Social Uplift

Help strengthen the collective cyber defences of all Australian organisations, contributing to a resilient ecosystem.

Thought Leadership
Keep up to date with our latest thought leadership articles on the CI-ISAC blog.
Our Services
The CI-ISAC leverages central resources and collective experience to support all members, regardless of maturity. This inclusive approach encourages all members to participate in cyber threat sharing.

Managed Threat Intelligence
Managed Threat Intelligence empowers members to effectively manage cyber risk.
Trusted Communities
Join trusted forums both within and across your industry sector to share best practices.

Powered by Partners
CI-ISAC partners with socially conscious organisations who are helping contribute
to the collective defences of our membership
Over 110 teams have already started working with us,
hear a selection of their member stories

CI-ISAC in the news
Browse a selection of our recent media coverage.
#strongertogether

CI-ISAC leverages membership fees to promote the collective uplift of all critical infrastructure defences, and as such members of all tiers gain access to the same core services and capabilities



You must be logged in to post a comment.